PURPLEHAZE
Security is not a fair fight.
PurpleHaze gives defenders back the advantage.
Running real penetration tests on demand and delivering validated, same-day reports directly from your environment.
Identify and prove exploitable paths before they’re used against you.
Real Attack Paths
Chains weaknesses the way attackers do.
Validated Reports
Same-day proof, not theoretical risk.
From Your Environment
Runs directly where risk lives.
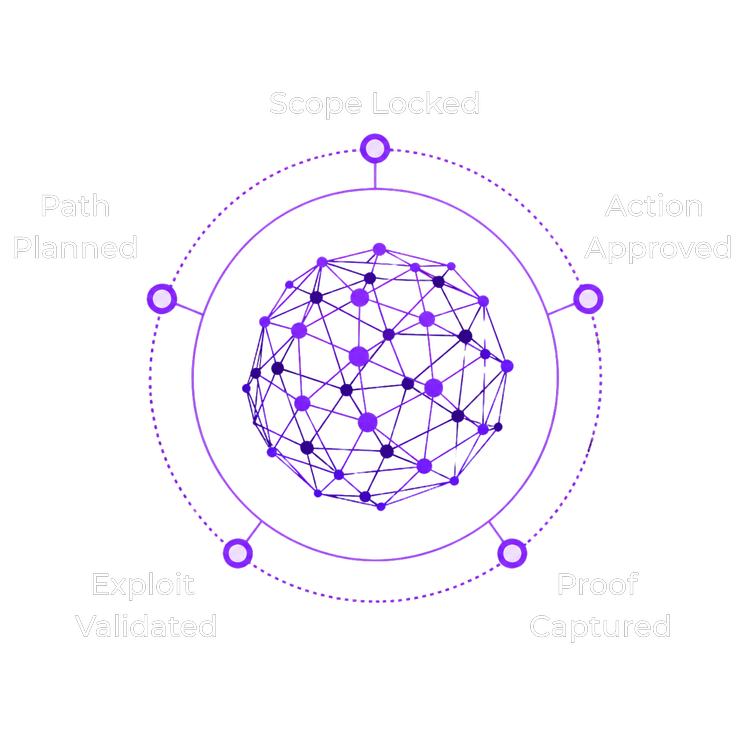
Agentic Offensive Operations You Define the Limits
Purple Haze plans and runs real attack paths at machine speed. Your team controls the scope, approvals, execution, and evidence from start to finish.
- Guardrails set before execution
- Approvals required before action
- Safe testing against live environments
- Deterministic actions with full audit trail
Built for Environments Others Cannot Touch
- Runs without cloud access
- Tests sensitive infrastructure safely
- Operates inside restricted networks
- Produces evidence without exposure
No cloud dependency.
No unnecessary data movement.

